A Sophisticated Crime Ring Exploits Telecom Logistics
A customer eagerly refreshes their FedEx tracking page, waiting for their brand-new iPhone to arrive. The estimated delivery time approaches, but the package never shows up. Instead, it has already been intercepted by a sophisticated crime ring—one that used a mix of software scraping, bribery, and on-the-ground theft to steal thousands of devices before they even reached customers’ doorsteps.
The recent wave of organized porch piracy targeting high-value telecommunications shipments exposes vulnerabilities in delivery tracking systems, retailer security, and carrier logistics. This theft operation not only resulted in financial losses but also raised serious concerns about fraud prevention, cybersecurity, and consumer trust within the telecom industry.
How the Crime Ring Pulled Off the Heist
Unlike the common image of porch pirates opportunistically snatching packages off doorsteps, this group operated at an entirely different level of sophistication. Here’s how they executed their operation:
- Automated Scraping of Delivery Tracking Systems
The crime ring developed software to scrape tracking numbers from FedEx’s website, bypassing security measures meant to limit mass data requests. This allowed them to monitor shipment routes and delivery schedules in real time. - Bribing Telecom Employees
AT&T store employees were paid thousands of dollars to provide order details and delivery schedules. Some were even recruited to bring in additional accomplices, expanding the operation’s reach within the carrier network. - On-the-Ground Theft Operations
Dispatchers within the crime ring coordinated teams to intercept packages moments before delivery. Once stolen, the iPhones were quickly funneled through unauthorized retail channels, including international markets. - Dropoff Points and Distribution
A Brooklyn-based storefront served as a central hub for stolen goods before they were shipped abroad. Investigators uncovered direct ties between the store’s owner and prior fraud cases involving stolen telecom devices.
Risks to Brand Reputation
This incident highlights the urgent need for telecom providers, logistics companies, and retailers to reinforce their security measures and fraud detection systems. The risks extend far beyond financial losses—telecom operators must also consider brand reputation, customer trust, and regulatory compliance.
1. Strengthening Cybersecurity in Tracking Systems
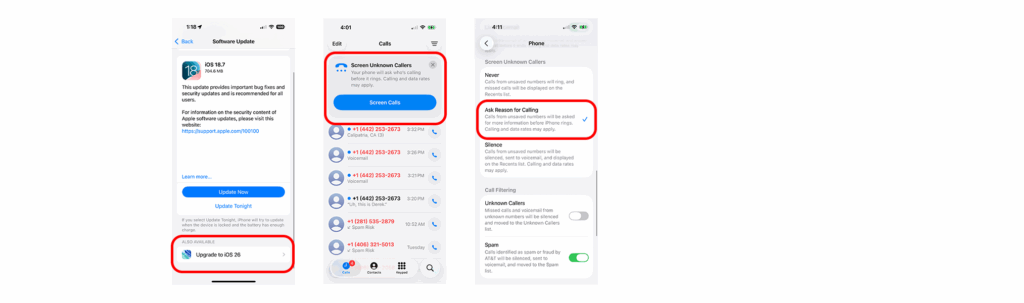
Delivery tracking platforms must enhance their security protocols to prevent unauthorized data scraping. Implementing CAPTCHAs, rate limiting, and AI-driven fraud detection can help identify and block suspicious activity.
2. Improved Employee Screening & Insider Threat Management
The involvement of bribed employees underscores the need for strict background checks, ongoing monitoring, and fraud prevention training in retail and carrier operations.
3. Enhancing Last-Mile Delivery Security
Retailers and carriers can implement measures such as multi-factor authentication for pickup, live delivery tracking with secure handoff requirements, and geofencing alerts to reduce the risk of package interception.
4. Strengthening Consumer Protection Measures
Customers should be educated on secure delivery options like requiring signatures, using secure lockers, and leveraging AI-powered fraud detection in their telecom account management systems.
The Rise of Organized Crime in Package Theft
The rise of organized crime in package theft isn’t an isolated issue—it’s a wake-up call for the telecommunications industry. As 5G networks expand and e-commerce drives higher demand for doorstep deliveries, security challenges will only grow.
Telecom operators, logistics providers, and regulators must collaborate to enhance fraud prevention, leverage AI-driven security solutions, and adapt to evolving threats in an increasingly digital-first world.
By addressing these vulnerabilities today, the industry can stay ahead of future risks and protect both businesses and consumers from the next wave of high-tech porch piracy.
sources
www.msn.com/en-us/money/companies/how-bribes-helped-a-crime-ring-steal-thousands-of-iphones-from-porches/ar-AA1B9QK7
appleinsider.com/articles/25/03/19/how-a-porch-piracy-gang-stole-thousands-of-iphones-in-a-sophisticated-crime-spree
www.wsj.com/us-news/how-bribes-helped-a-crime-ring-steal-thousands-of-iphones-from-porches-8d9f02f1?mod=telecom_news_article_pos1